How the $2 Trillion AI Infrastructure Boom, Federal Surveillance Networks, and Ransomware Attacks on Cities Threaten Your Connected Home
Executive Summary
You’re sitting in your smart home. Your Ring doorbell watches the street. Your Nest thermostat learns your patterns. Your Alexa listens for commands. Your smart TV knows what you watch. Your fitness tracker counts your steps. Your smart refrigerator tracks your diet.
The AI Data Center Gold Rush: When $1+ Trillion in Investments Meets Community ResistanceThe 2025 Infrastructure Boom, Trump’s AI Executive Orders, and the Fight Over America’s Electricity and Water Executive Summary In January 2025, President Trump stood in the White House flanked by Sam Altman (OpenAI), Larry Ellison (Oracle), and Masayoshi Son (SoftBank) to announce what he called “the largest AI infrastructure project![]() Security Careers HelpSecurity Careers
Security Careers HelpSecurity Careers
But here’s what you didn’t know:
- Your doorbell footage may be accessible to U.S. Customs and Border Protection through secret partnerships with 80,000+ AI cameras nationwide
- Your smart home data is being used to train Meta’s AI models without meaningful consent
- Your city’s infrastructure is under constant ransomware attack, with 34% of municipalities hit in 2024
- Your IoT devices fall under the EU Data Act (Sept 12, 2025) requiring manufacturers to give you access to your device data
- Your connected home is only as secure as the city infrastructure supporting it
This article connects three converging threats to your smart home:
- The AI Data Center Boom: Tech giants investing $2+ trillion in infrastructure that consumes your data to train AI models
- The Federal Surveillance Expansion: CBP, FBI, and other agencies gaining access to private surveillance networks
- The Municipal Cyber Collapse: Ransomware crippling city services your smart home depends on
The uncomfortable truth: Your smart home isn’t a sanctuary. It’s a data collection node in a surveillance infrastructure you never consented to join, powered by AI data centers draining community resources, all while the municipal services you depend on are collapsing under cyberattacks.
Part I: Your Smart Home is Training AI (Whether You Know It Or Not)
The Data Your Devices Generate
Let’s catalog what your smart home produces every single day:
Amazon Ring/Nest Doorbell:
- Video footage of everyone who approaches your door
- Facial recognition data
- License plate numbers from cars on your street
- Timestamps of when you come and go
- Audio recordings of conversations near your door
Smart Speakers (Alexa, Google Home, Siri):
- Voice recordings of every command
- Background conversations (when wake word detected)
- Household routines and schedules
- Shopping habits and preferences
- Music and media consumption
Smart Thermostat (Nest, Ecobee):
- When you’re home vs. away
- Sleep schedules
- Temperature preferences
- Energy usage patterns
- Occupancy patterns room-by-room
Smart TV (Samsung, LG, Roku):
- Every show and movie you watch
- How long you watch
- When you watch
- Viewing habits and patterns
- Voice commands if enabled
Fitness Trackers / Smartwatches:
- Sleep patterns
- Exercise routines
- Heart rate and health data
- Location tracking
- Daily movement patterns
Smart Appliances:
- Refrigerator: Food inventory, shopping patterns
- Washer/Dryer: Usage times, household size indicators
- Coffee Maker: Wake-up times, consumption habits
- Vacuum (Roomba): Floor plans of your home
Security Systems:
- Entry/exit patterns
- Motion detection events
- Window/door sensor activations
- Camera footage (interior and exterior)
Where This Data Actually Goes
Here’s the journey of your smart home data:
Step 1: Device Collection Your device collects data and sends it to manufacturer’s cloud servers
Step 2: Cloud Processing Data stored in AWS, Azure, or Google Cloud data centers
- Each device generates 1-5GB per month
- Multiply by your devices: 10 devices = 10-50GB/month
- Multiply by millions of homes
Step 3: AI Training Meta announced it’s building:
- Hyperion data center (Louisiana): 5 gigawatts, training AI on your data
- Prometheus (Ohio): 1+ gigawatt, powering “personal superintelligence”
- $600 billion investment through 2028: All to process YOUR data
Amazon, Google, Apple doing the same:
- Amazon: $100+ billion in AI infrastructure
- Google: $75 billion globally
- Apple: $500 billion over four years
What they’re training:
- Recommendation algorithms (what you should buy/watch next)
- Predictive models (anticipating your needs before you express them)
- Behavioral analysis (understanding household patterns)
- Voice recognition improvement
- Computer vision models (recognizing objects, people, activities)
The Privacy Illusion
You think: “I can turn off data sharing in settings”
Reality:
- Meta’s privacy policies are deliberately vague
- Opt-out mechanisms are “cumbersome” and “not guaranteed to succeed”
- Even if you opt out, metadata is still collected
- Cross-device tracking connects your home data to your phone, computer, social media
EU Data Act (September 12, 2025) gives you rights:
- Access data your devices generate
- Port data to third parties
- Prevent vendor lock-in
In practice:
- Most Americans don’t have these rights (no U.S. federal equivalent)
- Companies make exercising rights difficult
- Data already collected doesn’t disappear
The Environmental Cost of Your Smart Home’s AI Appetite
Your 10 smart devices generating 50GB/month doesn’t sound like much.
But multiply across 100 million smart homes:
- 5 exabytes of data per month
- Requires massive data centers to process
- Memphis xAI Colossus: 1 million gallons of water daily for cooling
- Meta Louisiana: 5 million gallons daily when complete
- Electricity: Your data processing contributes to 12% of U.S. electricity consumption by 2030
Your community pays the price:
- Memphis residents: 79% increase in air pollution from AI data center
- El Paso: 1.5 million gallons daily water consumption from Meta data center
- Louisiana: Ratepayers subsidizing power plants for Meta
You’re not just sharing data. You’re funding environmental destruction of communities you’ve never heard of.
Part II: The Federal Surveillance Network You’re Already Part Of
The Flock Safety Revelation (August 2025)
U.S. Customs and Border Protection secretly accessed 80,000+ AI cameras nationwide through “pilot programs” local police departments didn’t even know they were participating in.
The cameras: Automated License Plate Readers (ALPRs) from Flock Safety
The data collected:
- Every license plate passing by
- Vehicle make, model, color
- Location and timestamp
- Can track vehicles across vast geographic areas
The scope:
- 80,000+ cameras in over 2,000 cities across 42 states
- Direct CBP backend access (not case-by-case requests)
- 25 Colorado departments agreed to share
- Many departments didn’t know about federal access
What went wrong:
- Illinois Secretary of State alleged illegal data sharing violating state privacy laws
- State law prohibits sharing license plate data with police investigating out-of-state abortions or undocumented immigrants
- Flock Safety suspended all federal agency partnerships after violations surfaced
What this means for your Ring doorbell:
- If Flock cameras can be federally accessed, why not Ring?
- Amazon Ring has 400 partnerships with law enforcement
- No warrant required for many access requests
- Data shared includes footage of YOUR street, YOUR visitors, YOUR family
Your Smart Doorbell as Law Enforcement Tool
Amazon Ring partnerships with police:
- 400+ law enforcement agencies partnered
- Officers can request footage from any Ring in area
- You get notification, can decline
- BUT: Amazon can share without your consent in “emergencies”
What counts as “emergency” (per Amazon’s terms):
- “Danger of death or serious physical injury”
- Defined by Amazon, not you
- No warrant required
- You may never know footage was shared
The expansion:
- Google Nest has similar partnerships
- Arlo, SimpliSafe, others joining
- Your entire neighborhood becomes surveillance grid
Combine with ALPR data:
- CBP tracks vehicle arriving at your house via Flock cameras
- Requests Ring footage showing who exited vehicle
- Facial recognition identifies individual
- Complete surveillance without single warrant
The Smart Home Metadata Dragnet
Even if you disable cameras, you’re generating metadata:
When does your smart lock engage? = When you’re home/away When does thermostat shift to “away mode”? = Travel patterns When does doorbell motion stop detecting? = Bedtime When does smart coffee maker activate? = Wake time
Law enforcement doesn’t need video. Metadata tells the story.
Fourth Amendment challenges:
- Supreme Court ruled GPS tracking requires warrant (Carpenter v. U.S.)
- But smart home data comes from “third party” (Amazon, Google)
- “Third-party doctrine” = No reasonable expectation of privacy
- Your data is fair game for subpoenas
Part III: When Your City’s Infrastructure Collapses, Your Smart Home Fails Too
The 2025 Municipal Cyber Siege
Summer 2025 was devastating for U.S. cities:
Nevada (August 2025):
- Statewide ransomware shutdown
- DMV, state agencies, phone lines down
- Employee accidentally downloaded malware in May
- Went undetected for months
- Cost: $1.3 million (just contractor assistance)
Columbus, Ohio (July 2024):
- Rhysida ransomware demanded $1.9M
- City refused to pay
- Hackers leaked personal data of 500,000 residents
- Services disrupted for weeks
Cleveland Municipal Court (February 2025):
- Qilin ransomware, $4M demand
- Systems offline nearly 3 weeks
- Trials hampered, employees without internet
Attleboro, Massachusetts (November 2025):
- Multiple IT systems crippled
- City and police phone lines down
- Email services offline
- Staff reverted to paper
- Interlock ransomware claimed 66,000 files stolen
The pattern: 34% of state/local governments hit by ransomware in 2024, mean recovery cost $2.83M (double from 2023)
How Municipal Attacks Affect Your Smart Home
Your smart home depends on city infrastructure:
- Internet connectivity: City-owned fiber, municipal broadband
- Emergency services: 911 dispatch, police/fire response
- Utilities: Water, electricity, gas management systems
- Traffic: Smart city traffic lights, parking
- Public safety: Gunshot detection, flood warning systems
When city gets ransomed:
Scenario: City traffic management system encrypted
- Your Ring doorbell can’t warn you of approaching emergency vehicles
- Your smart car’s traffic avoidance relies on city data feeds (gone)
- Your home automation “away mode” based on city occupancy sensors (offline)
Scenario: City water system compromised
- Your smart irrigation system gets no water pressure data
- Your leak detection system can’t differentiate city issue from home issue
- Your water quality monitor has no municipal baseline
Scenario: City power grid monitoring down
- Your home battery system (Tesla Powerwall) can’t coordinate with grid
- Your EV charging schedule optimized for grid load (can’t access data)
- Your HVAC system’s “grid-aware” features useless
Real example: Memphis Community Against Pollution:
- xAI’s Colossus consuming 40% of city power at full capacity
- Grid already unstable (2022 rolling blackouts during cold snap)
- Your smart home’s power reliability directly tied to city’s ability to manage AI data center load
The Smart City Attack Surface
Modern cities run on IoT infrastructure:
Traffic Management:
- Connected traffic lights
- Real-time traffic monitoring
- Parking sensors and meters
- License plate readers (like Flock)
Public Safety:
- Gunshot detection (ShotSpotter)
- Emergency call systems
- First responder coordination
- Surveillance camera networks
Utilities:
- Smart water meters
- Grid management systems
- Automated leak detection
- Energy monitoring
All of these are HACKABLE.
Ransomware gangs target cities because:
- Limited cybersecurity budgets
- Outdated systems
- Pressure to restore services quickly (likely to pay)
- Critical infrastructure = high stakes
When city systems fall, your smart home loses its “intelligence” because it’s not actually intelligent—it’s dependent on cloud services, internet connectivity, and municipal infrastructure.
Part IV: The Compliance Maze Nobody Understands
GDPR Doesn’t Protect Americans
Europe has:
- GDPR: Comprehensive data protection
- EU Data Act (Sept 12, 2025): IoT device data rights
- Strong enforcement (€20M or 4% revenue fines)
Americans have:
- State-by-state patchwork
- No federal IoT privacy law
- Weak enforcement
- Corporate-friendly regulations
The State Privacy Law Maze
19 U.S. states have comprehensive privacy laws by 2025:
States with privacy laws: California, Virginia, Colorado, Connecticut, Utah, Iowa, Indiana, Tennessee, Montana, Oregon, Texas, Delaware, New Hampshire, New Jersey, Maryland, Minnesota, Nebraska, Kentucky, Rhode Island
What they cover: Varies wildly
Example confusion:
- California CCPA: Broad consumer rights, can opt out of data sales
- Texas: 30-day cure period before enforcement
- Utah: More business-friendly, fewer consumer rights
Your smart home manufacturer:
- Must comply with all 19 states if operating nationally
- Usually implements “lowest common denominator” approach
- You get minimal protections even in strong-law states
What You Actually Have Rights To
Under strongest state laws (California, Virginia, Colorado):
- Right to know: What data is collected
- Right to access: Get copy of your data
- Right to delete: Request deletion (with exceptions)
- Right to opt-out: Of data sales (not collection)
- Right to correct: Inaccurate data
- Right to port: Take data to competitor
Limitations:
- Doesn’t apply to data already used for AI training
- “Legitimate business purposes” exception
- De-identification loophole
- No private right of action (can’t sue directly in most states)
The EU Data Act vs. American Reality
EU Data Act** (September 12, 2025)**:
For smart home owners:
- Unrestricted access to data generated by your devices
- Right to share data with third parties
- Prevent vendor lock-in
- Manufacturers must provide data portably
- Fair, reasonable, non-discriminatory access
Example: Your Nest thermostat data must be accessible to you in format another thermostat company can use. Switch vendors without losing historical data.
In America: No equivalent. You’re locked into ecosystem. Historical data stays with manufacturer.
Why this matters:
- Can’t switch from Amazon ecosystem to Google without losing everything
- No competition = no pressure to improve privacy
- Manufacturer controls your data forever
Part V: Practical Defense - What You Can Actually Do
The Harsh Reality: You Can’t Win, But You Can Fight Back
Accept these truths:
- If you want smart home convenience, you WILL share data
- That data WILL be used for AI training
- Law enforcement CAN access it
- Your city’s infrastructure WILL be attacked
- You cannot achieve perfect privacy
But you can minimize harm.
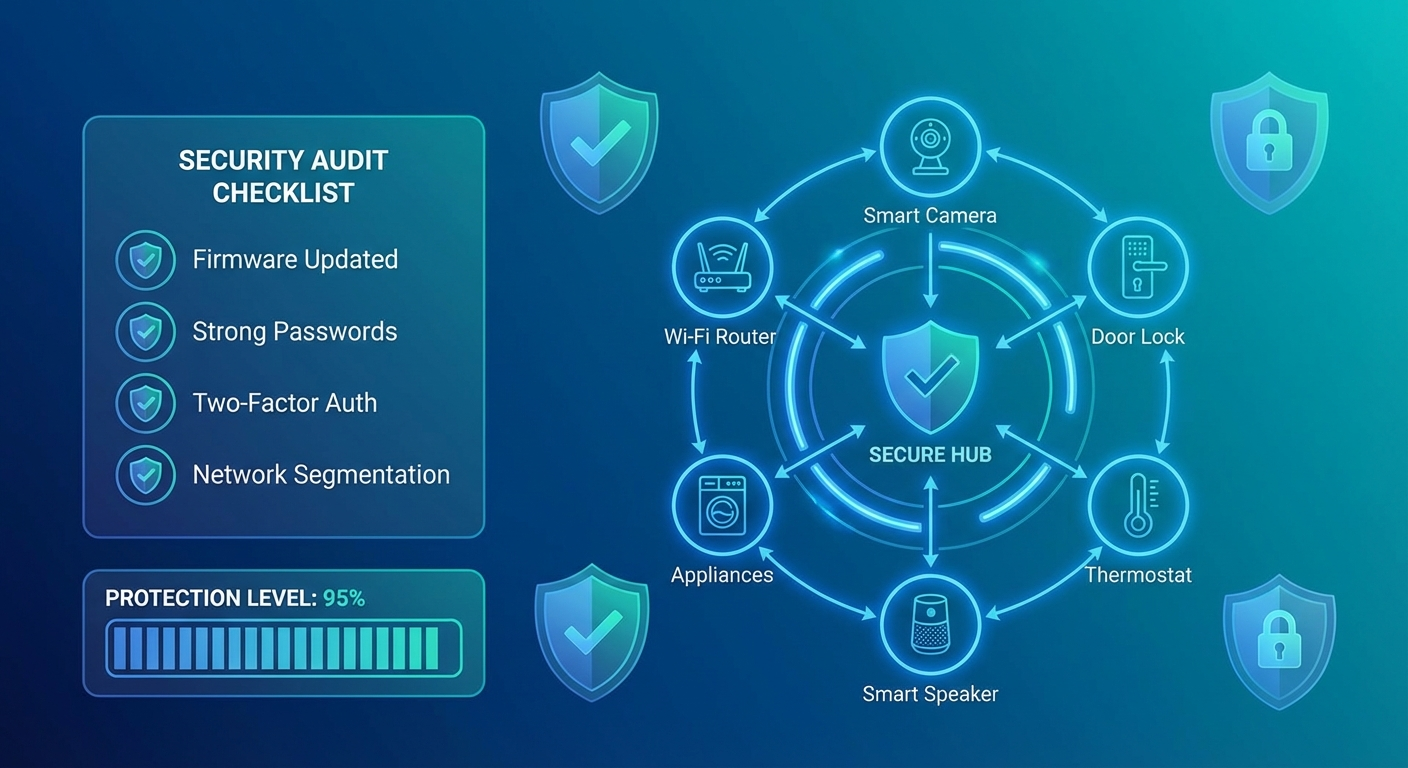
Tier 1: Essential Protections (Do These First)
1. Audit Your Devices
Make a list:
- What smart devices do you have?
- What data does each collect?
- Where does data go?
- Can you live without it?
Kill 30-50% of devices. Seriously.
Questions to ask:
- Do I REALLY need smart light bulbs? (No, use dumb bulbs with smart switch)
- Do I REALLY need smart refrigerator? (No, regular fridge works fine)
- Do I REALLY need always-listening smart speaker? (No, use phone for commands)
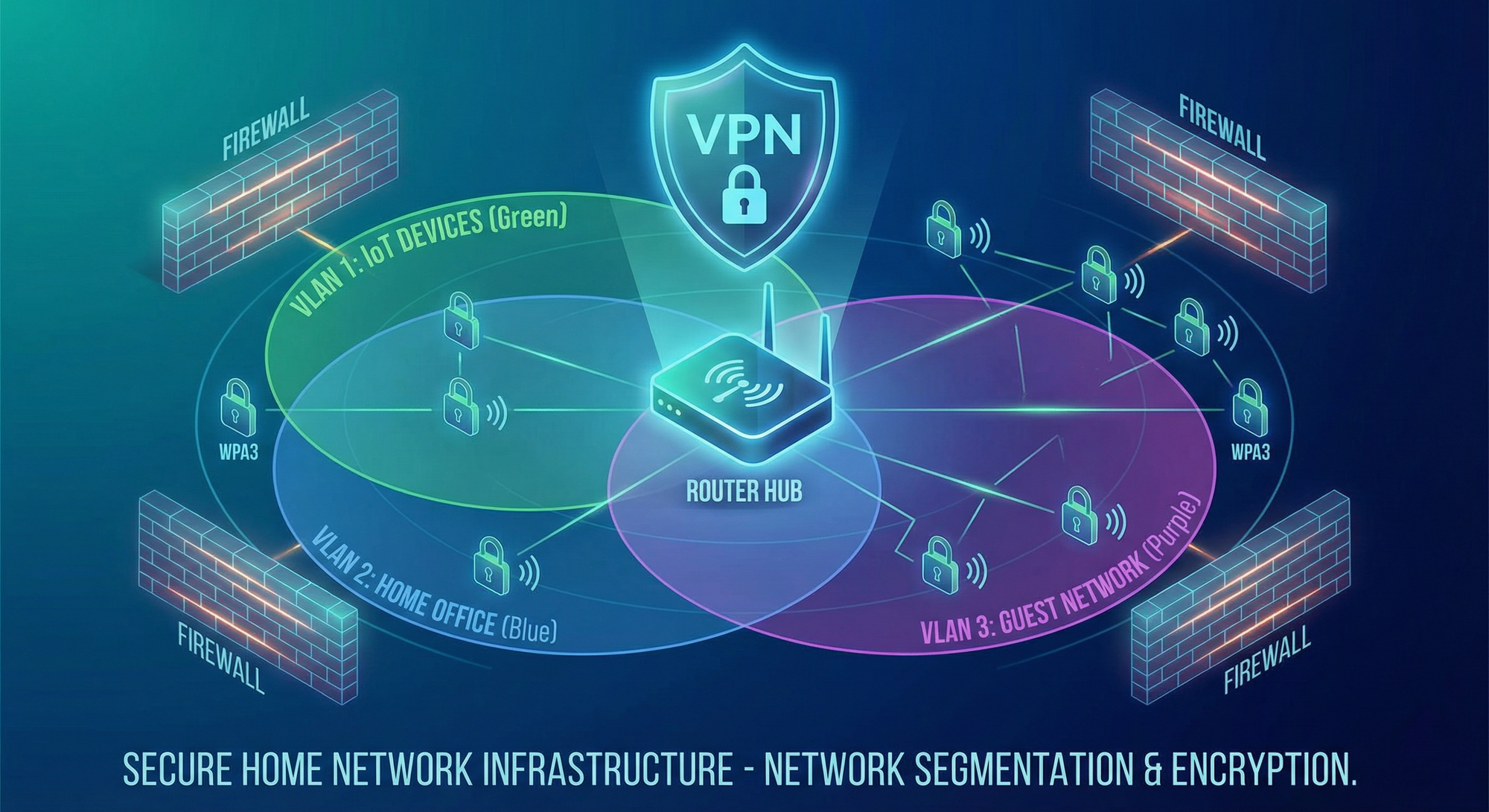
2. Network Segmentation
Set up 3 separate WiFi networks:
Network 1: Secure (WPA3 encryption)
- Your phone
- Your computer
- Your tablets
- Nothing else
Network 2: IoT Quarantine (WPA2, guest network)
- Smart TV
- Smart speakers
- Smart appliances
- Cannot access Network 1
Network 3: Security Cameras (isolated VLAN if possible)
- All cameras
- Cannot access internet except for viewing
- Block manufacturer cloud upload if possible
Why this matters: When your smart TV gets hacked, it can’t access your laptop’s bank accounts.
3. Camera Discipline
Indoor cameras: DON’T.
Seriously, don’t put cameras inside your house. You’re inviting surveillance.
If you must:
- Cover when not needed
- Disable audio
- Local storage only (no cloud)
- Review who has access monthly
Outdoor cameras:
- Point at YOUR property, not neighbor’s
- Disable audio (avoid recording conversations)
- Local storage preferred
- If cloud, enable two-factor authentication
- Review footage sharing permissions
Ring/Nest specific:
- Decline all law enforcement requests
- Disable “motion sharing” with neighbors
- Turn off “community safety” features
- Consider switching to local-only cameras (Ubiquiti, Reolink NVR)
4. Voice Assistant Discipline
The only safe smart speaker is no smart speaker.
If you must have one:
- Use mute button religiously
- Only unmute when giving command
- Mute immediately after
- Delete voice history monthly (in app settings)
- Disable “improve products” data sharing
- Don’t put in bedroom or bathroom (for fuck’s sake)
Better alternative:
- Use phone’s voice assistant
- Phone is with you, not always listening in every room
- Easier to verify what’s being recorded
5. Review Privacy Settings
Monthly task (set calendar reminder):
For each device:
-
Open companion app
-
Go to Privacy Settings Opt out of EVERYTHING possible:
-
Marketing
-
Analytics
-
Product improvement
-
Research
-
Sharing with “partners”
-
Delete historical data
-
Disable voice recordings if option exists
Why monthly? Companies reset settings after updates. Check religiously.
Tier 2: Advanced Protections (For the Paranoid)
6. Self-Hosted Smart Home
Ditch cloud services entirely:
Home Assistant (open source):
- Runs on Raspberry Pi or NUC
- Controls smart devices locally
- No cloud connection required
- Your data never leaves your house
Compatible with:
- Zigbee devices (Philips Hue, IKEA)
- Z-Wave devices
- Many WiFi devices (with local control enabled)
Learning curve: Steeper, but worth it for privacy
7. VPN for IoT Devices
Set up VPN at router level:
- Entire network tunneled through VPN
- Hides smart home traffic from ISP
- Obscures location data
Recommended VPN providers (no logs policy):
- Mullvad
- ProtonVPN
- IVPN
Caveat: Some devices won’t work with VPN (geolocation required). May need split tunneling.
8. Pi-hole DNS Filtering
Block tracking and ads at network level:
- Raspberry Pi running Pi-hole software
- Filters DNS requests
- Blocks known tracking domains
- Works for ALL devices on network
Bonus: Your smart TV’s constant “phone home” gets blocked. It cries for attention and gets none.
9. Firmware Auditing
Check for firmware updates monthly:
- Manufacturers patch vulnerabilities
- But also add “features” (aka more tracking)
Pro move: Read update notes before installing
- Look for “improved analytics”
- Look for new “cloud features”
- Consider NOT updating if adding tracking
Balance: Security fixes vs. privacy invasion
10. Data Request Everything
Exercise your state privacy rights:
California residents (CCPA):
- Submit data access request to every smart device manufacturer
- See what they actually have
- Request deletion
- Document their response
Others: Check your state’s privacy law, submit requests where available
Why bother?
- You learn what they collect
- You exercise your rights (use it or lose it)
- You cost them time/money (natural deterrent to excessive collection)
Tier 3: Nuclear Options (Going Off-Grid)
11. Dumb Home Best Home
Controversial take: Ditch smart devices entirely.
Replace with:
- Regular thermostat (programmable, not internet-connected)
- Regular lights (with timers if needed)
- Regular door locks (they’ve worked for 100 years)
- Regular security system (local alarm, no cameras)
- Regular TV (not “smart”)
What you lose: Convenience What you gain: Privacy, security, lower electricity bill, fewer subscriptions
**12. Faraday Cage Your Home
Just kidding. Don’t do this. You need WiFi. But the mental image is fun.
Part VI: The Municipal Defense - Protecting Your City Protects Your Home
Why You Should Care About City Cybersecurity
Your city’s security directly affects your smart home.
When Columbus, Ohio got ransomed:
- Traffic systems disrupted
- Emergency services coordination affected
- Utility billing systems offline
- 500,000 residents’ data leaked
If your city is next:
- Your smart home’s city-dependent features fail
- Your emergency alert systems may not work
- Your utilities may be unstable
- Your data may be exposed
How to Help Your City
1. Attend City Council Meetings
Ask these questions:
- What’s our cybersecurity budget?
- When did we last test our incident response plan?
- Do we have cyber insurance? How much coverage?
- What IoT devices do we use for city services?
- Who manages security for those devices?
- Do we have contracts with Flock Safety or similar surveillance tech?
- What data sharing agreements exist with federal agencies?
2. Vote for Cybersecurity Funding
When bond measures come up:
- Support IT infrastructure improvements
- Support cybersecurity training for staff
- Support redundancy and backup systems
It’s not sexy spending, but it protects your smart home’s dependencies.
3. Demand Transparency
File FOIA requests (Freedom of Information Act):
- Request copies of surveillance technology contracts
- Request data sharing agreements with law enforcement
- Request cybersecurity audit results (some will be redacted, that’s fine)
- Request incident response plans (what happens when attacked?)
Sunshine is the best disinfectant. Cities that know residents are watching tend to be more careful.
4. Support Local Journalism
Investigative journalists uncover:
- Undisclosed surveillance contracts (like Flock/CBP)
- Security vulnerabilities in city systems
- Lack of incident response planning
Subscribe to local news, even if it costs $5/month. Worth it to know what your city is doing with your data and your tax dollars.
Part VII: The Future Nobody Wants
The Trajectory We’re On
By 2030 if nothing changes:
AI Data Centers:
- 12% of U.S. electricity consumption
- 1,068 billion liters of water annually
- Trillions in investment, communities bearing environmental costs
Smart Home Ubiquity:
- 500+ million U.S. smart home devices
- Every device feeding AI training
- Complete behavioral profiles of every household
Surveillance Expansion:
- Federal access to all major surveillance platforms
- Facial recognition on every doorbell
- Location tracking from every connected car
- Metadata dragnet covering everyone
Municipal Collapse:
- 50%+ of cities hit by ransomware annually
- Critical services disrupted regularly
- Smart city infrastructure regularly compromised
- Your smart home fails when city fails
Regulatory Capture:
- Federal privacy law written by tech companies
- Weak enforcement
- Pre-emption of strong state laws
- No meaningful consent requirements
This is dystopia achieved through convenience.
The Future We Could Have
With strong action:
Federal Privacy Law (modeled on GDPR + EU Data Act):
- Comprehensive data rights
- IoT data ownership rights
- Strict limitations on AI training
- Strong enforcement
Municipal Cybersecurity Mandate:
- Federal funding for city cybersecurity
- Mandatory training and audits
- Incident response requirements
- Shared threat intelligence
Surveillance Oversight:
- Warrant requirements for smart home data
- Ban on federal backdoor access to private surveillance
- Transparency in law enforcement technology contracts
- Community consent requirements
Environmental Justice:
- AI data centers must prove community benefit
- Water usage limits in drought areas
- Air quality monitoring and enforcement
- Ratepayer protections from infrastructure costs
AI Training Consent:
- Explicit opt-in for AI training use
- Ability to withdraw data from models
- Compensation for data used in training
- Transparency in how data is used
How We Get There
1. Individual Action:
- Implement protections above
- Exercise your privacy rights
- Cost companies time and money
2. Community Action:
- Attend city council meetings
- Demand transparency
- Support local journalism
- Organize with neighbors
3. Political Action:
- Support candidates who prioritize privacy
- Support federal privacy legislation
- Support municipal cybersecurity funding
- Oppose surveillance expansion
4. Economic Action:
- Boycott worst privacy offenders
- Support privacy-respecting alternatives
- Vote with your wallet
- Demand better from manufacturers
Conclusion: Your Home, Your Data, Your Choice
Your smart home is not a standalone island. It’s a node in a vast network of:
- AI data centers draining community resources
- Federal surveillance programs you never consented to
- Municipal infrastructure under constant attack
- Corporate data collection without meaningful oversight
Every device you add to your home is a choice:
- Convenience vs. privacy
- Cloud features vs. local control
- Free service vs. data as payment
- Smart integration vs. independence
The default path leads to total surveillance. The comfortable path. The convenient path.
The alternative path requires work:
- Auditing your devices
- Segmenting your network
- Reading privacy policies
- Exercising your rights
- Attending city meetings
- Supporting regulation
But it’s the only path that preserves your autonomy.
Your smart home should serve you. Not train AI models. Not feed surveillance networks. Not depend on ransomed city infrastructure.
Make it smart on YOUR terms.
Essential Resources
Privacy Assessment and Tools:
- Personal Privacy Self-Assessment Quiz
- Complete Guide to Personal Privacy Tools 2025
- Smart Home Device Security Quiz
Surveillance and Federal Access:
- Federal Surveillance: CBP’s 80,000+ Camera Network
- Meta AI Privacy Controversy
- 10 Key Privacy Developments 2025
Compliance and IoT Rights:
- EU Data Act Compliance Guide
- EU Data Act September 12 Implementation
- U.S. State Privacy Law Navigator
- GDPR vs CCPA vs LGPD Comparison
Municipal Cyber Threats:
- The Cyber Siege: Ransomware Crippling America’s Cities
- Attleboro Cyberattack (November 2025)
- Ransomware Onslaught October 2025
- 2025 Cybersecurity Landscape Briefing
AI Data Center Investigation: